Mobile Device Management Settings 101
Terms every iOS developer should understand

I am a Software Engineer working on open source and enterprise mobile SDKs for iOS and MacOS developers written in Swift. From 🇩🇪 and happily living in 🇺🇸
This blog post will introduce the most important terms and concepts. It is a summary of the Apple Platform Deployment guide and other articles.
Don't get confusing by other abbreviations of similar nature. Here is a quick cheat sheet.
- Mobile Device Management (MDM): focus on tracking, managing and securing mobile devices
- Mobile Application Management (MAM): focus on controlling access to enterprise applications and the data associated with them (not the whole device)
- Unified Endpoint Management (UEM): focus not only on classical mobile devices but all sorts of devices, including Internet of Things (IoT)
- Enterprise Mobility Management (EMM): combines MDM & MAM
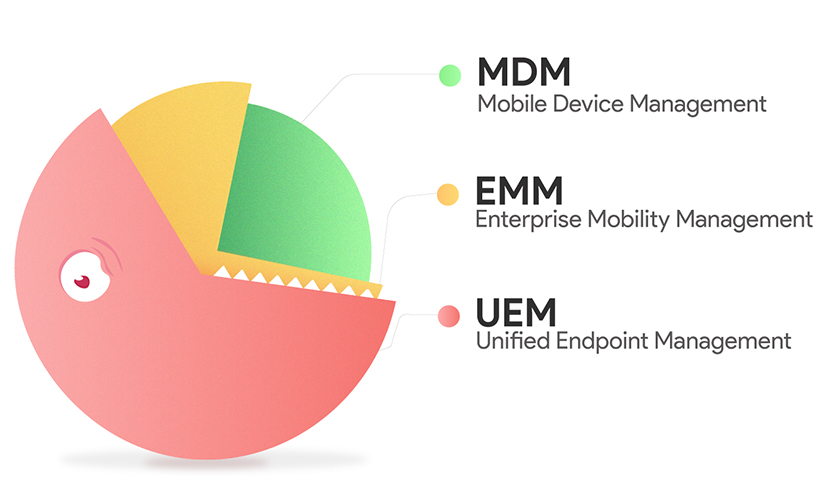
Image Source: https://www.hexnode.com/blogs/mastering-mobility-management-mdm-vs-emm-vs-uem/
Intro to Mobile Device Management
iOS, iPadOS, macOS, and tvOS have a built-in framework that supports mobile device management (MDM).
A company wants to make sure that mobile devices used by its employees are secure and managed in a unified way. For example, all devices should run a specific iOS version as a minimum OS version.
How can this be achieved?
Devices can be managed if those are enrolled in a Mobile Device Management solution (e.g. Jamf Now, VM Airwatch, ...)
Enrollment
| Type | Description |
| User Enrollment | designed for BYOD—or bring-your-own-device deployments—where the user, not the organization, owns the device. Requires Managed Apple IDs |
| Supervision | allows organizations to have users manually enroll devices into a mobile device management (MDM) solution and then manage many different aspects of device use, including the ability to erase the device. |
| Automated Device Enrollment | designed for devices owned by the organization. Automated Device Enrollment lets organizations configure and manage devices from the moment the devices are removed from the box. You can also use all of the available payloads and restrictions defined by Apple, and you have the option to prevent the MDM enrollment profile from being removed by the user. |
Ok, so either the company IT administrator or the user will enroll devices into a Mobile Device Management (MDM) solution.
The following standard capabilities shall be enforceable by the company IT administrator:
- updating software and device settings
- monitoring compliance with organizational policies
- remotely wiping or locking devices.
How can such processing of managed devices work no matter the actual MDM solution?
Unified MDM protocol
Independent of the vendor, all MDM solutions operate on the same protocol!
Apple's Mobile Device Management (MDM) protocol defines a standardized way for system administrators to send either profiles or commands securely and wirelessly to a managed device.
Wireless communication is done through Apple’s Push Notification Server (APNS).
There are two types of profiles:
- Enrollment profile
- Configuration profile
More in the next chapter.
Enrollment profiles
An enrollment profile is a configuration profile with an MDM payload that enrolls the device in the MDM solution specified for that device. This allows the MDM solution to send commands and configuration profiles to the device, and to query certain aspects of the device. When a user removes an enrollment profile, all configuration profiles, their settings, and managed apps based on that enrollment profile are removed with it. There can be only one enrollment profile on a device at a time.
After the enrollment profile is approved, either by the device or the user, configuration profiles containing payloads are delivered to the device.
Configuration Profiles
A configuration profile is an XML file (ending in .mobileconfig) that consists of payloads that load settings and authorization information onto Apple devices. Configuration profiles automate the configuration of settings, accounts, restrictions, and credentials. These files can be created by an MDM solution or Apple Configurator 2, or they can be created manually.
A configuration profile
- can have more than one payload
- can be encrypted and signed
- restrict-able to a specific device
- can change settings for an entire device or for a single user
- device profiles
- user profiles
Payloads
A payload can be configured to manage specific settings on Apple devices. For example, you can have different payloads require a complex passcode, populate an Exchange account with all the Exchange server information, and add a VPN configuration to a device
After payloads are configured, they are saved in a configuration profile.
In some cases, they work only on devices that are supervised.
Restrictions
Restrictions can be enabled—or in some cases, disabled—by administrators to help prevent users from accessing a specific app, service, or function of an iPhone, iPad, iPod touch, Mac, or Apple TV that’s enrolled in an MDM solution. For example, a restriction can be added that prevents an iPhone, iPad, or Mac from using the camera to take pictures or videos. Certain restrictions on an iPhone may be mirrored on a paired Apple Watch.
MDM commands
MDM solutions can send commands to enrolled Apple devices. Commands can trigger software updates, locate misplaced devices with Lost Mode, or install apps remotely. To learn which MDM commands are supported for your devices, consult your MDM solution's documentation. For more information, see MDM commands for Apple devices.
Query and reporting services
An MDM solution can query Apple devices for various information, including hardware serial number, device UDID, Wi-Fi, Media Access Control (MAC) address, and FileVault encryption status (for Mac computers). It can also query for software information, such as device version and restrictions, and list the apps installed on the device. For more information, see Device information MDM queries for Apple devices.
Managed Apps
Managed apps are distributed via MDM technology and can be configured and reassigned by MDM.
Managed apps can be removed from a device remotely by the MDM solution or when a user removes a device from MDM. On iOS and iPadOS devices, removing an app also removes its associated data in its data container.
Managed apps can have several MDM capabilities and restrictions, providing improved security and a better user experience. Examples:
- Use app configuration settings: App developers can identify configuration settings that can be set before or after the app is installed as a managed app. For example, a developer could specify a SkipIntro setting to have the app skip intro screens for the managed app.
- App version updates: Periodically check the App Store for new versions of apps, then send an install app command to the device to update the app. This check also applies to Custom Apps. Device-assigned apps installed and managed through MDM must be updated by MDM; no app update notifications are shown to users in the App Store.
App developers can define what settings can be pre-configured by an MDM server for their app. For example, you could deploy an app with a pre-populated server URL, so users only need to enter their username and password to get the app up and running.
Read my article about Managed App Configuration for more details.
Appendix
I recommend these additional sources:
- Mobile device management (MDM) for iOS by Diksha Bhargava
- Mobile Device Management 101 by Jamf
- Apple Device Management for Beginners by Jamf



